IBM launch SysFlow cybersecurity tool
IBM Research have announced that they have submitted their SysFlow systems monitoring project to the open source community. The company claim that SysFlow is a system which has…

IBM Research have announced that they have submitted their SysFlow systems monitoring project to the open source community. The company claim that SysFlow is a system which has been designed to detect cyber attacks more precisely than conventional telemetry tools.
IBM stated that SysFlow connects the behavior of processes to both network and file access activities, thereby affording users greater visibility of cloud workloads by providing a broader analytic context to more effectively spot attacks on corporate networks.
IBM Research claim that the SysFlow surveillance suite is an adaptable and multi-functional tool, capable of being used in diverse situations such as threat surveillance, protecting the integrity of containers as well as delivering investigative capacities in the event of suspected cyber attacks. The representation of the activities of a system is encoded in a compact format which records how applications interact with their environment.
The aim of opening the SysFlow libraries and format is to facilitate their integration with custom analytical microservices and open source frameworks, such as Scikit-learn or Spark.
IBM Research state that the different stages of the attack chain are precisely mapped by SysFlow, with SysFlow describing the relationships between processes, files, containers and terminals as flows (volumetric operations) and events (single operations).
IBM claim that presenting the data in a graph form enables end users to quickly find security information, helping detection by automated defenses as well as allowing for rapid intervention against attacks.
SysFlow has a data processing pipeline that provides a set of APIs and reusable components. These components allow telemetry probes to be deployed to monitor cloud workloads and also export data and records to object storage services where the data can be analyzed.
IBM Research is seeking input and comments from the open source community on the SysFlow system, which the company freely admits is a work in progress.
Related articles

Supply Chain – The shift from ‘Just-in-Time’ to ‘Just-in-Case’
Supply chain management is undergoing a profound structural transformation in March 2026. After years of the just-in-time model…
Read More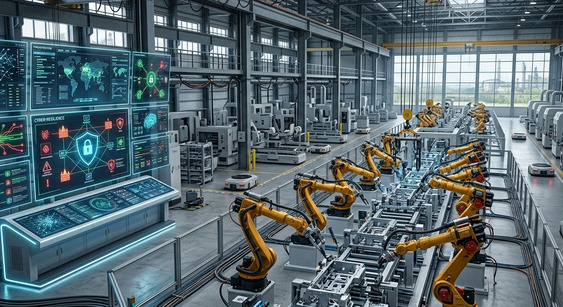
Industry 4.0 and the challenge of cyber resilience
Industry 4.0 - The 2026 edition of the Global Industrie trade fair, held in Paris from 17 to…
Read More
The end of traditional just-in-time: the rise of strategic stockpiling
The traditional model of just-in-time and zero inventory came under serious scrutiny in mid-March 2026. The constant volatility…
Read More
